Using PowerShell for automation is a common way for IT teams to automate tasks on Windows. You can manage but, as helpful as PowerShell can be for automation, it's got one major drawback: It only works in Windows environments. But with one free tool – Puppet Bolt – you can mix PowerShell tasks with tasks in other languages on Linux, opening a whole new avenue of time-saving automation.
In this blog post, we’ll share some of the benefits of using PowerShell and Bolt together, and then walk you through restarting a service with a PowerShell script and Bolt.
What is PowerShell?
PowerShell is a task automation tool and configuration management framework from Microsoft that is built on the .NET Common Language Runtime (CLR).
IT teams working in Windows can use PowerShell to create automation scripts for common or repetitive tasks and configure systems for repeatable testing and deployments.
Back to topIs PowerShell Good for Automation?
PowerShell is great for automating common tasks in a strictly Windows domain environment. But if you need to perform tasks in a mixed Windows/Linux environment, you’ll need to add another tool like Puppet Bolt to your regular scripting.
Additionally, if you need to orchestrate various parts of a complex workflow, PowerShell on its own won't be enough.
Puppet Bolt is a cross-platform, easy-to-use, agentless automation tool from Puppet that allows you to automate tasks on an as-needed basis or as part of a greater orchestration workflow. You can use Bolt to patch and update systems, troubleshoot servers, deploy applications, or stop and restart services – and you can use in Bolt with PowerShell for better, more powerful automation.
How Does Bolt Work with PowerShell for Automation?
With Bolt, you have the ability to mix PowerShell tasks with tasks in other languages on Linux, all in the same workflow – one that is version controlled and easily distributable.
Even if you don't have a mixed environment, Bolt allows you to easily share small reusable tasks written in PowerShell, instead of your team members having to re-implement common functionality in their scripts.
Get Your Hands on Easy Automation with Puppet Bolt
Additionally, Bolt plans – which go beyond the scope of the example in this blog post – allow you to add Puppet module code via Apply manifest blocks, giving you the ability to mix imperative tasks with declarative state configuration, using Puppet-supported modules or PowerShell DSC via the dsc_lite module.
Back to topDid you know you can use PowerShell Modules just like a Puppet module? Check out our guide on using resources from the PowerShell Gallery right in Puppet
PowerShell for Automation Examples + One to Try Yourself
With PowerShell for automation, you can automate backups, provision VMs, monitor and restart services, and more.
PowerShell for automation use cases cover Windows system administration, managing server configurations, deploying, and reporting on system resources.
To see Bolt in action, we’ll walk you through a simple example that involves running a script with Bolt, converting the script to a Bolt task, and then executing the task.
How to Run a PowerShell Script that Restarts a Service
The example script we’ll use, called restart_service.ps1, performs a common task of restarting a service on demand.
Before You Begin
- Ensure you’ve already installed Bolt on your Windows machine.
- Identify a remote Windows node to work with.
- Ensure you have Windows credentials for the remote node.
- Ensure you have configured Windows Remote Management on the remote node.
1. Run a PowerShell Script on a Remote Windows Node
First, we’ll use Bolt to run the script as-is on a single target node.
2. Create an Inventory File to Store Information About the Node
Create a Bolt project directory to work in, called bolt-guide. Copy the restart_service.ps1 script into bolt-guide. In the bolt-guide directory, run the restart_service.ps1 script with the following command:
bolt script run .\restart_service.ps1 service=W32Time --nodes winrm://uia27aaq2e10fa6 -u Administrator -p Note: The -p option prompts you to enter a password.
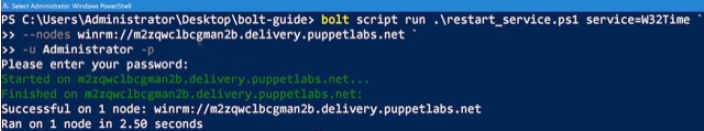
To have Bolt securely prompt for a password, use the --password or -p flag without supplying any value. Bolt then prompts for the password, so that it does not appear in a process listing or on the console. Alternatively, you can use the prompt plugin to set configuration values via a prompt.
You now have an inventory file to store information about your nodes.
You can also configure a variety of options for Bolt in bolt.yaml file, including global and transport options.
3. Convert Your Script to a Bolt Task
To convert the restart_service.ps1 script to a task, giving you the ability to reuse and share it, you create a task metadata file. Task metadata files describe task parameters, validate input, and control how the task runner executes the task.
Note: This guide shows you how to convert the script to a task by manually creating the .ps1 file in a directory called tasks. Alternatively, you can use Puppet Development Kit (PDK), to create a new task by using the pdk new task command. If you’re going to be creating a lot of tasks, PDK is worth getting to know. For more information, see the PDK documentation.
- In the bolt-guide directory, create the following subdirectories:
bolt-guide/
└── modules
└── gsg
└── tasks- Move the
restart_service.ps1script into thetasksdirectory. - In the
tasksdirectory, use your text editor to create a task metadata file – named after the script, but with a.jsonextension, in this example,restart_service.json. - Add the following content to the new task metadata file:
{
"description": "Stop or restart services using an existing PowerShell script.",
"input_method": "powershell",
"parameters": {
"service": {
"description": "List of service names to stop.",
"type": "Array[String]"
},
"norestart": {
"description": "Restart the service immediately. Maps to PowerShell [switch].",
"type": "Boolean",
"default": false
}
},
"supports_noop": false
} - Save the task metadata file and navigate back to the
bolt-guidedirectory.
You now have two files in the gsg module’s tasks directory: restart_service.ps1 and restart_service.json -- the script is officially converted to a Bolt task. Now that it’s converted, you no longer need to specify the file extension when you call it from a Bolt command.
- To validate that Bolt recognizes the script as a task, run the following command:
bolt task show gsg::restart_servicegroups: - name: windows nodes: - - config: transport: winrm winrm: user: Administrator Password: config: transport: winrm winrm: user: Administrator Password:
Congratulations! You’ve successfully converted the restart_service.ps1 script to a Bolt task.
4. Execute Your New Task
To execute your new task, run the following command:
bolt task run gsg::restart_service service=W32Time --nodes windowsNote:
--nodes windowsrefers to the name of the group of target nodes that you specified in your inventory file.
That’s it! You now have an automated workflow for restarting a service on-demand on multiple target nodes. You can use this same workflow to run your other PowerShell scripts on an inventory of remote nodes.
See the Bolt command reference for more information about the commands you used in this guide.
Back to topExplore Your Automation Options
As mentioned at the start of this blog post, if you want to take this automation framework further, you can combine multiple tasks into a Bolt plan. Plans give you the ability to create multi-server workflows involving multiple tasks and Puppet code.
Bolt is a great place to start your automation journey, but if you have a large organization spanning multiple teams, Puppet Enterprise gives you more control over and insight into the automation of your infrastructure and provides a flexible combined agentless and agent-based approach.
Ready to try out Puppet Enterprise? Get started with a free trial today!
Learn More
- How to simplify your workflow with agentless automation
- Download this ebook: How Self-Service Automation Drives Team Velocity and Business
- Check out this podcast episode about PowerShell Gallery DSC Resources
- Learn more about Puppet and PowerShell DSC integrations
- Get tips on how to do automation the right way