Installing software and managing services across multiple Windows machines can be a nightmare — if done manually. Thankfully, Puppet can automatically install and update Windows software and ensure services are configured correctly across multiple machines in your infrastructure.
Windows Configuration Management Tools
There are multiple ways to do configuration management on Windows, including SCCM (now Microsoft Configuration Manager), which is a proprietary Windows product, and other IT automation and configuration management solutions like Puppet.
Examples of Windows configuration management tools include:
- Microsoft Configuration Manager (formerly SCCM): Microsoft Configuration Manager is a Windows-native product that allows IT to deploy, update, manage, and configure systems on Windows.
- PowerShell Desired State Configuration (DSC): This feature in PowerShell enables automation of Windows and Linux OS configurations.
- Puppet: Puppet automation for Windows powers Windows configuration management with infrastructure as code.
- Chef: Chef can automate system configurations on Windows servers.
- Ansible: Ansible's WinRM protocol allows IT to automate tasks that can help them manage Windows systems.
Configuration management is a pretty important part of managing infrastructure. A configuration management tool monitors for changes to your systems and hardware, detects configuration drift (deviations from your desired state), and corrects errors. Some configuration management tools can even correct drift automatically. That's especially helpful for systems running on Windows.
On Windows, configuration management can be a bit of a bear. Tools like Microsoft Configuration Manager (SCCM) exist in the proprietary space, but other solutions for Windows configuration management have popped up. Chocolatey is one of the most popular package management tools for Windows (Puppet also integrates smoothly with Chocolatey).
The point is that sysadmins and other IT professionals have several options for doing configuration management on Windows. Picking the right one for your organization's IT will depend on the scale, complexity, and needs of your infrastructure.
- Related ▶️: How Puppet Supports DevOps Workflows in the Windows Ecosystem
- Related 📄: Puppet on Windows
Examples of Windows Configuration Management
On Windows, configuration management tools can be used to deploy software, apply patches, manage users, backup data, standardize configurations, and more.
As mentioned, configuration management can be difficult on Windows compared to *nix environments. But it's still possible, and configuration management can help you control and maintain your Windows environment and meet your internal requirements.
Here are some examples what you can do with Windows configuration management:
- Deploy software
- Apply and manage patches
- Standardize configurations
- Enforce configurations in compliance with industry regulations
- Manage users, groups, and permissions
- Monitor and report on performance
- Harden system security
- Provision new servers and workstations
- Backup and restore data and configurations
How to Do Windows Configuration Management in Puppet
There are two ways to automatically install Windows applications using Puppet:
- Run a simple software install through Puppet
- Have Puppet use Chocolatey to install software
In this example, we’ll have Puppet install some software using Chocolatey.
The process is simple and can be done through the Puppet dashboard, an easy-to-learn GUI. In this example, we’ve already set up a group of Windows servers with Puppet agents installed, and we've installed and configured Chocolatey.
Installing Software on Windows with Puppet and Chocolatey
First, launch Puppet and create a group for your Windows servers. Groups define the requirements for server membership, and in this instance, we’ll choose Windows machines. Next, we'll use some Puppet facts for Windows to filter out the machines we don't need. I'll use osfamily = windows in order to make sure all of my Windows nodes receive the classification that I'm going to apply.
Once we’ve selected the type of machines we’ll be addressing, we can apply a class to them that will tell Puppet to run the software installation. We’re using the Chocolatey class, which defines our software installation. Once we apply that class to the machines in our group, we can trigger a Puppet run and our software will be installed silently in the background.
With Windows you usually run a simple command from PowerShell or the command line when you're trying to apply these package changes. Puppet, however, lets you specify and bundle all the packages that you would like to see in your Windows system. In this case we're actually going to be managing Notepad++, Firefox, Google Chrome and a plugin.
Let’s look at the Puppet code behind the Chocolatey class to see how it works:
class tse_windows::choco {
package { ‘notepadplusplus’:
ensure => latest,
provider => ‘chocolatey’,
}
package { ‘firefox’:
ensure => latest,
provider => ‘chocolatey’,
}
package { ‘flashplayerplugin’:
ensure => latest,
provider => ‘chocolatey’,
}
package { ‘googlechrome’:
ensure => latest,
provider => ‘chocolatey’,
}
}The Puppet code specifies the Chocolatey package. If you need to change any of it, you only do it once in Puppet and the changes will be applied across your entire infrastructure when Puppet runs.
Managing Windows Services in Puppet
Monitoring and managing services can be tedious in a large Windows environment. With Puppet, you can interrogate systems to see how resources are being used and managed. In this example we’ll examine the automatic update service, called wuauserv in Puppet.
Currently the service is stopped, but that can easily be changed in the Puppet code. It’s just a simple matter of changing the enabled parameter to true.
service { ‘wuauserv’:
ensure => ‘running’,
enable => ‘false’,
}
service { ‘wuauserv’:
ensure => ‘running’,
enable => ‘true’,
}When we run Puppet, the change will be made on one machine in our group, however the number of machines doesn’t matter — the same code can be used to update 1,000 machines or more.
WSUS and Puppet
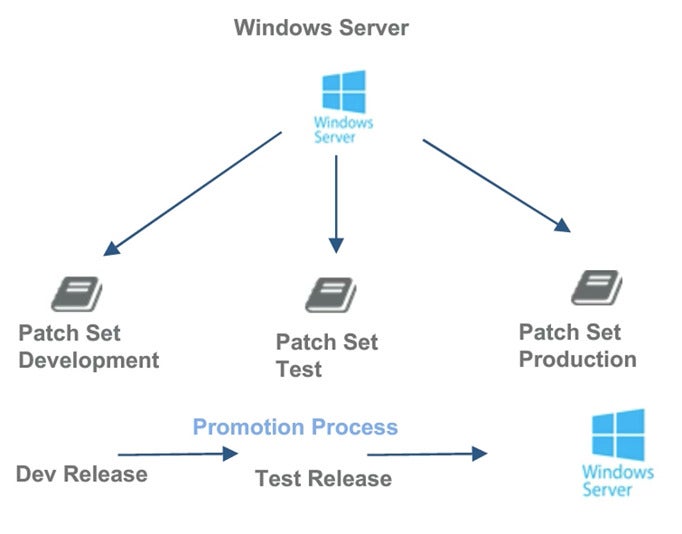
Puppet can easily manage Windows patching and hot fixes in a Windows environment. This diagram shows how you can use Puppet to move a patch from development to testing to production.
And this is the sample code:
class { “wsus_client’:
server_url => “http://myserver:8530’,
auto_update_option => “Scheduled”,
scheduled_install_day => “Tuesday”,
scheduled_install_hour => 2,
}With Puppet you can schedule the install date and the time to avoid interruptions or disruptions to the flow of your business.
Learn More
- How to use Puppet for Oracle configuration management
- Read about the challenges of container configuration
- How to install Hyper-V on Windows
- How Red Hat Satellite + Puppet can coexist in support of configuration management